Aim:
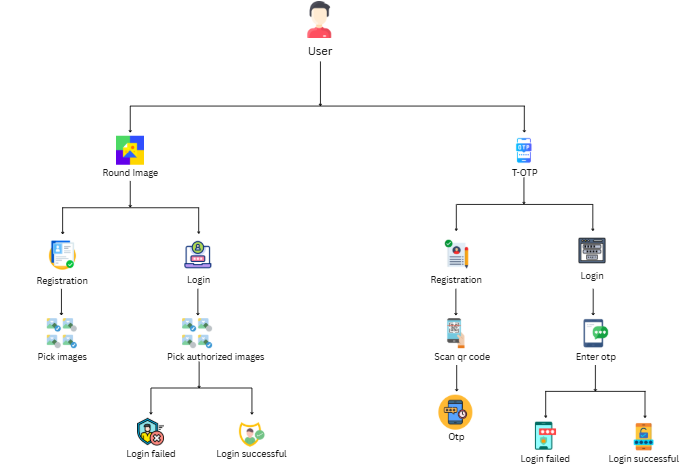
Our study aims to develop a Multi-Factor Authentication System that integrates RoundImage-based graphical password verification with Time-based One-Time Password (T-OTP) authentication to ensure secure, reliable, and observation-resistant user login. The system is designed to enhance trust, prevent unauthorized access, and reduce credential-based attacks by providing a tamper-resistant, user-friendly, and highly secure authentication framework suitable for modern digital environments, including IoT and web applications.
Abstract:
This project introduces a dual-layer authentication system integrating the RoundImage graphical password scheme with Time-based One-Time Password (T-OTP) verification. RoundImage improves security through multi-round image selection, reducing vulnerability to shoulder-surfing and brute-force attacks. Its fault-tolerant matching enhances usability, especially in lightweight IoT environments. To extend protection beyond knowledge-based credentials, the system adds T-OTP as a second factor. T-OTP generates time-synchronized dynamic codes, preventing unauthorized access even if images are observed. The hybrid model combines something you know (image rounds) with something you have (OTP token). A complete web-based prototype includes registration, graphical login, QR code generation, and OTP verification. Users follow a secure onboarding process with image credential creation and authenticator app setup. The system achieves low login error rates, strong memorability, and high resistance to observation attacks. Performance evaluation shows that combining RoundImage with T-OTP greatly reduces credential compromise risks. The architecture is optimized for distributed IoT environments with minimal computational overhead. Comparative analysis confirms improved security over single-factor graphical or password-only schemes. The interface design ensures usability for both novice and experienced users. Overall, the integration provides a secure, efficient, and user-friendly authentication method. The framework offers a foundation for enhancements such as adaptive security levels. This work demonstrates a balanced security–usability model using multi-round images and dynamic OTP verification.
Proposing System:
The proposed system introduces a hybrid authentication model that combines the RoundImage graphical password scheme with Time-based One-Time Password (T-OTP) verification. RoundImage strengthens security by requiring multi-round image selection, making it extremely resistant to shoulder-surfing and brute-force attacks. Its built-in fault-tolerant matching ensures that users can authenticate successfully even if minor selection errors occur. The system further enhances protection with T-OTP codes, providing a dynamic second factor that refreshes every 30 seconds. This dual-layer approach ensures that even if graphical credentials are observed, attackers cannot access the system without the time-sensitive OTP. A web-based interface enables secure registration, QR code generation, image-based login, and OTP verification. The architecture is optimized for both web and IoT environments, ensuring lightweight and efficient performance. Through this integrated multi-factor design, the proposed system delivers high security without compromising user convenience.
Advantages:
The proposed system provides strong protection against shoulder-surfing, brute-force attempts, and observation-based attacks. Users benefit from improved memorability due to visual-based authentication combined with fault-tolerant logic. The addition of T-OTP ensures a second independent security layer, significantly reducing unauthorized access risk. The interface remains simple and user-friendly, making the system suitable for all types of users. Overall, the hybrid model offers a secure, practical, and highly reliable authentication solution.



















Reviews
There are no reviews yet.